Automate phishing training, your way
Whether you prefer fully AI-driven adaptive training or being more hands-on, Hoxhunt powers your security training with flexible automation. Our gamified approach engages employees, equips them to combat sophisticated threats, and (measurably) reduces risky behaviors at scale.









Enable one-click phishing reporting, build lasting habits



Maximize engagement with personalized simulations at scale



Show results with powerful dashboards



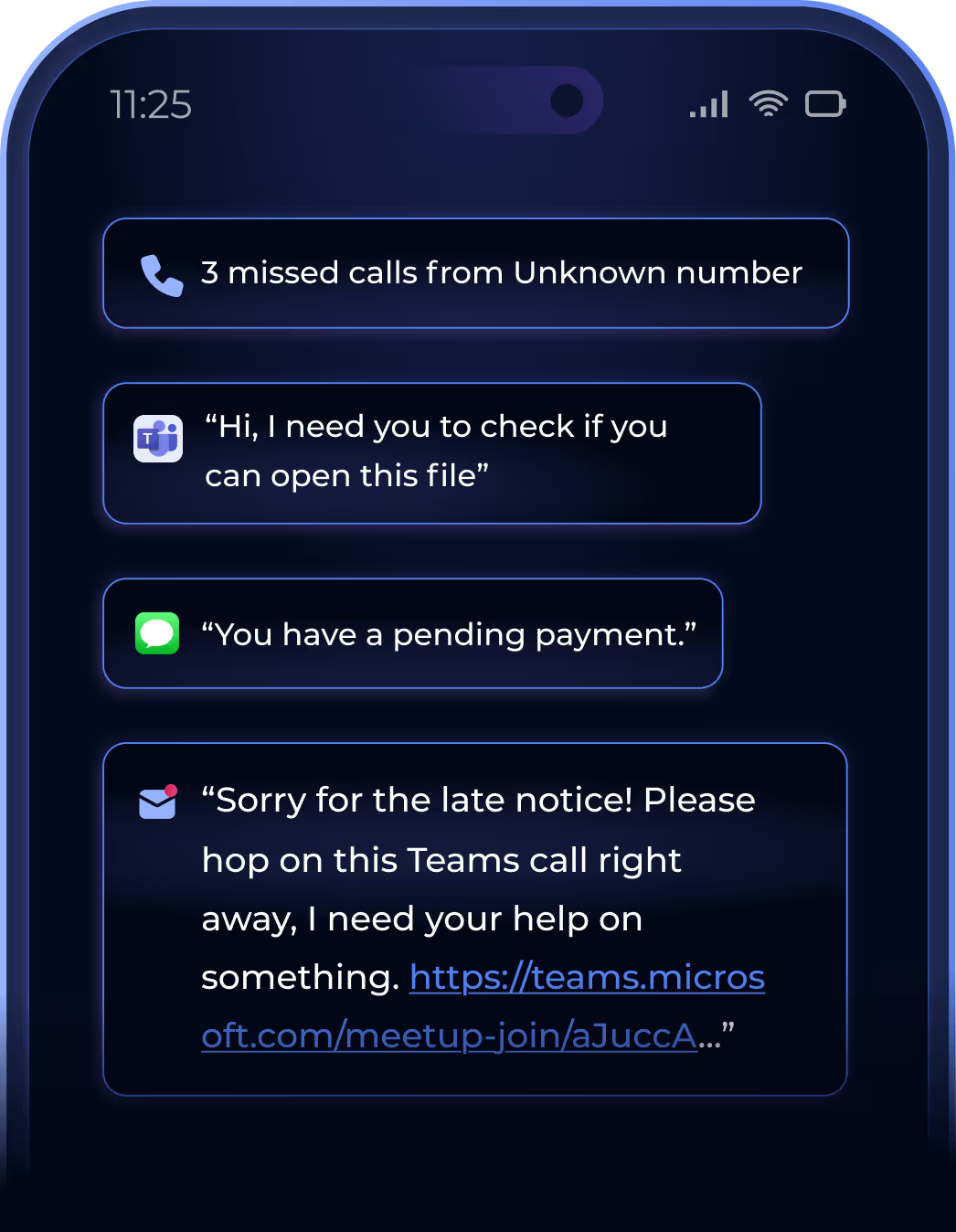
Go beyond email phishing
Deepfake phishing attacks
A custom multi-step experience featuring a deepfake of an authoritative figure.
Smishing
SMS phishing sent with customized text messages, including reporting on iOS.
Vishing
Callback simulations and voice cloning.
MS Teams phishing
Phishing messages sent within your trusted communication environment.
Choose your automation level
Simulate realistic phishing attacks with constantly updated training content based on the latest threats.

Personalize and deliver the training using AI

Manage the phishing training in your way
Phishing training for employees FAQ

Hoxhunt automatically creates individual learning paths for each employee and selects simulated phishing campaigns based on the employee's skill, role, and location.
Employees receive gamified cyber threat simulations and interactive training on their weakest skills roughly every 10 days.
This approach ensures employees are well-prepared to recognize and report real-world suspicious emails and other types of phishing attacks.

Adaptive phishing training delivers better outcomes because phishing simulations are personalized to every individual and delivered automatically at the right time and frequency.
Hoxhunt leverages AI to automate the entire phishing training lifecycle, so security teams can personalize user training at scale with fewer resources and measurably reduce their organization's risk profile.

Yes, hundreds of global organizations train millions of employees with Hoxhunt.
Simulated phishing campaigns are translated into 30+ languages, so global organizations can confidently train all of their employees with Hoxhunt.

Modern organizations switch to Hoxhunt to automate their entire security awareness and phishing training lifecycle and tangibly reduce human risk - all in one human risk management platform.
Legacy vendors require substantial resources to maintain and run effective phishing simulations at the frequency that habit-forming behavior change requires.
Unlike traditional vendors, Hoxhunt doesn’t just check a box; it measurably changes employee behaviors with training that employees genuinely enjoy.
Hoxhunt's AI-powered, adaptive phishing training delivers up to 40 times higher engagement rates than anyone else in the industry.
Real-time behavioral analytics provide security teams with next-level visibility into human risk, allowing them to form insights and track progress.

Pricing depends on the number of user licenses and the service level that best fits your organization’s needs to ensure that businesses of all sizes can implement effective anti-phishing training.

Very easy. Hoxhunt's dedicated Implementation Team helps organizations quickly get the ball rolling on phishing simulations and start improving their security posture.
The team will guide you through onboarding, including setting up integrations, best practices for rolling out to employees, and more.
Reviewers give Hoxhunt a 9.7 out of 10 for ease of setup, compared to KnowB4 (8.8) and Proofpoint (8.7).

Yes, Hoxhunt phishing training seamlessly integrates with both Office 365 and Google Workspace environments.
Organizations can add the Hoxhunt reporting plug-in to Microsoft Outlook or Gmail email clients to enable quick employee reporting of malicious emails and other types of phishing threats.
The Hoxhunt reporting plug-in supports multiple languages and is available across desktop, web browser, and Android and iOS mobile applications to simplify the detection and reporting of phishing attempts.
For more information, refer to the listings on Microsoft AppSource and the Google Workspace Marketplace.

Yes, Hoxhunt offers a vast library of training modules to ensure compliance across broad or industry-specific requirements, like HIPAA, GDPR, and many more.
Modules are translated into 30+ languages and can be assigned by country, industry, or department.
You can also customize your own training content.
This flexibility allows organizations to address specific compliance requirements while reinforcing their cybersecurity culture.
Phishing training designed for people. Built for enterprise.
Learn how Hoxhunt can effortlessly transform your training program and reduce your human cyber-risk.
Fill out the form to schedule a 30-minute chat with a product expert. We'll discuss challenges you would like to solve, show a walk-through of Hoxhunt features, and answer any questions.












